06
Zero Trust Architecture: Reinventing Modern Cybersecurity
Explore what Zero Trust Security is, the benefits of Zero Trust Network Access (ZTNA), and how to implement a Zero Trust model to protect digital assets.
Introduction
With cyber threats growing more sophisticated and traditional perimeter defenses becoming obsolete, organizations are turning to a more robust framework: Zero Trust Architecture (ZTA). This approach represents a paradigm shift in how we secure data, systems, and identities in today’s decentralized and hybrid environments.
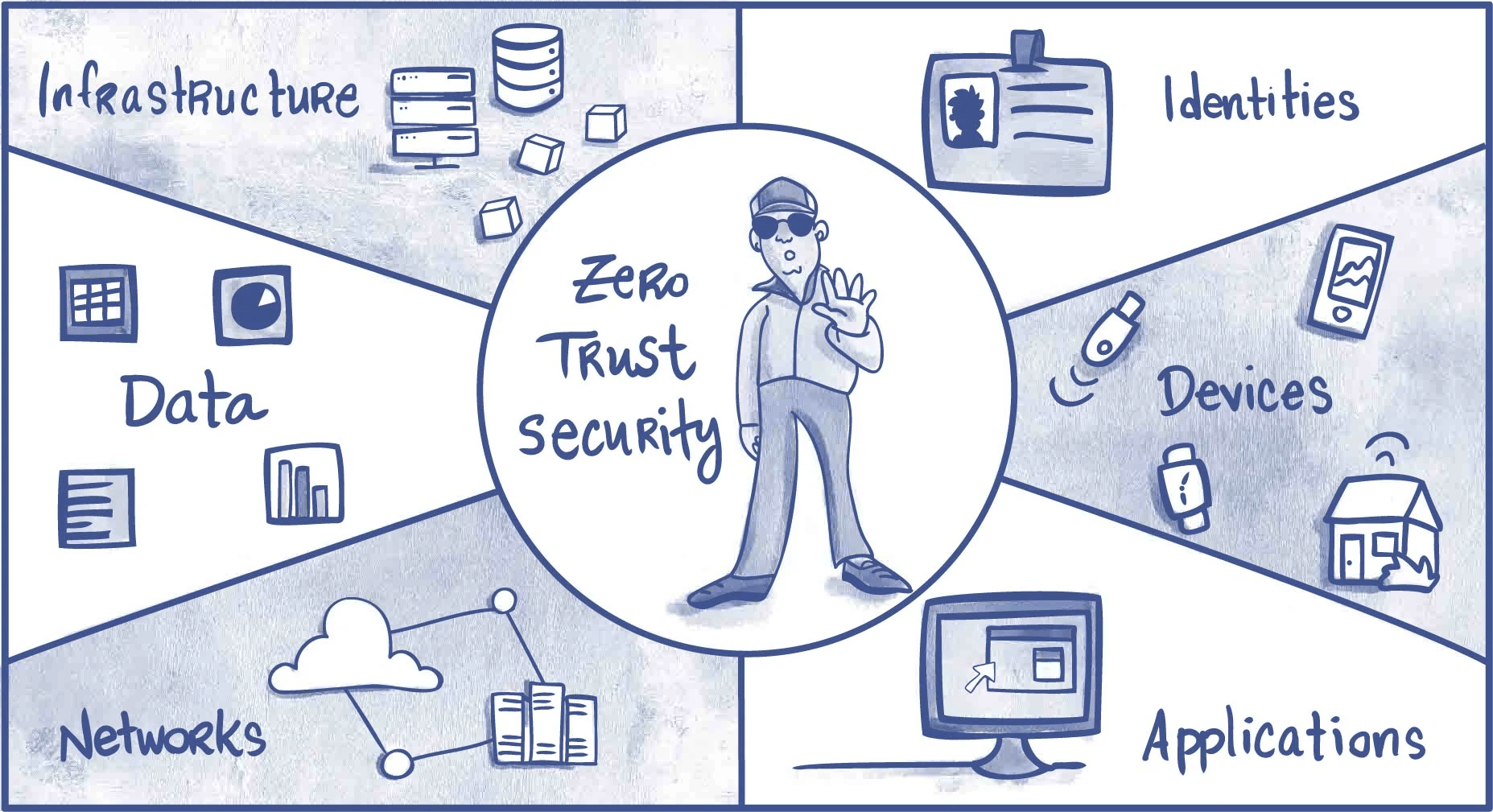
What is Zero Trust Security?
Zero Trust Security is a strategic approach that assumes no user, system, or application — whether inside or outside the network — is inherently trustworthy. It operates under the principle of “never trust, always verify,” requiring continuous authentication, strict access controls, and rigorous policy enforcement.
Unlike traditional models that focus on securing the perimeter, Zero Trust focuses on securing individual resources, reducing lateral movement within the network, and detecting abnormal behavior in real time.
Core Principles of Zero Trust
- Verify explicitly: Authenticate and authorize based on all available data points.
- Use least privilege access: Limit user and system permissions to the minimum required.
- Assume breach: Design defenses as if the attacker is already inside.
- Micro-segmentation: Break down networks into smaller zones to control traffic.
- Continuous monitoring: Use analytics to assess risk and behavior.
Benefits of Zero Trust
Implementing a Zero Trust model offers numerous advantages in modern cybersecurity environments:
- Stronger security posture: By eliminating implicit trust, organizations reduce the attack surface significantly.
- Protection against insider threats: Since every action is verified, malicious insiders are easier to detect and stop.
- Improved compliance: Helps meet regulatory requirements such as GDPR, HIPAA, and ISO 27001.
- Scalability: Especially effective in cloud-native and remote work environments.
- Enhanced visibility: Real-time insights into user behavior and device status.
Zero Trust Network Access (ZTNA)
Zero Trust Network Access (ZTNA) is a key component of Zero Trust Architecture. It enables secure access to applications without exposing them to the broader internet. Unlike traditional VPNs, ZTNA evaluates each access request based on context — such as user identity, device posture, and location — before granting access.
ZTNA solutions create a secure tunnel between the user and the application, allowing access only to specific services, not the entire network.
ZTNA vs Traditional VPN
| Feature | Traditional VPN | ZTNA |
|---|---|---|
| Access Scope | Full network | Per-app or per-resource |
| Trust Model | Implicit trust after login | Never trust, always verify |
| User Experience | Slow, needs configuration | Seamless and adaptive |
| Security Risk | Higher lateral movement | Minimized attack surface |
How to Implement a Zero Trust Model
Implementing Zero Trust isn’t a one-time project — it’s an ongoing strategy. Here’s a step-by-step approach to adopting Zero Trust in your organization:
Step 1: Identify the Protect Surface
Determine what you want to protect: sensitive data, applications, systems, and assets. Unlike the attack surface, the protect surface is small and specific.
Step 2: Map Data Flows
Understand how data moves across your network. This helps you identify communication paths and dependencies.
Step 3: Define Micro-Perimeters
Segment your network into smaller zones around each protect surface. Use next-generation firewalls or software-defined perimeters.
Step 4: Enforce Strict Access Controls
Apply the principle of least privilege. Use role-based access control (RBAC) and multi-factor authentication (MFA).
Step 5: Implement Continuous Monitoring
Use tools like SIEM (Security Information and Event Management) and UEBA (User and Entity Behavior Analytics) to monitor user and device activity in real time.
Step 6: Automate and Improve
Use automation for threat detection and incident response. Continuously refine your Zero Trust policies based on new insights and threats.
Common Challenges in Zero Trust Adoption
- Legacy infrastructure: Older systems may not support Zero Trust mechanisms.
- User resistance: Added layers of authentication can affect productivity.
- Complex implementation: Requires coordination across IT, security, and compliance teams.
- Cost considerations: Budgeting for new tools and ongoing maintenance.
Use Cases of Zero Trust
- Remote workforce: Secure access to internal apps without relying on perimeter-based VPNs.
- M&A integration: Securely connect third-party systems and users during mergers.
- Cloud migrations: Enforce identity-based access to cloud resources.
- Compliance: Achieve continuous compliance monitoring and data protection.
Conclusion: Zero Trust is the Future
As businesses continue to operate in cloud environments with distributed teams, traditional security models can no longer keep up. Zero Trust offers a holistic, modern approach that not only strengthens defenses but also aligns with compliance, business agility, and user experience.
Start by identifying your critical assets and incrementally building a Zero Trust Architecture. In the face of evolving cyber threats, trust nothing — verify everything.
Contact
Missing something?
Feel free to request missing tools or give some feedback using our contact form.
Contact Us